Random Key Generation Algorithm In C
Key generation is the process of generating keys in cryptography. A key is used to encrypt and decrypt whatever data is being encrypted/decrypted.

Some of the additional classes that I had to write to support the license key generation are a random number generator, a data type parser, a number display class, and a checksum class. The random number class uses the C# Random class but adds some additional methods to support the requirements. The methods are. Key generation is the process of generating keys for cryptography. The key is used to encrypt and decrypt data whatever the data is being encrypted or decrypted. Modern cryptographic systems include symmetric-key algorithms (such as DES and AES ) and public-key algorithms. /rhinoceros-5-license-key-generator-rhino.html.
- Jun 27, 2017 Pseudo Random Number Generator(PRNG) refers to an algorithm that uses mathematical formulas to produce sequences of random numbers. PRNGs generate a sequence of numbers approximating the properties of random numbers. A PRNG starts from an arbitrary starting state using a seed state.Many numbers are generated in a short time and can also be.
- Nov 04, 2014 The RSA Encryption Algorithm (2 of 2: Generating the Keys) Eddie Woo. Unsubscribe from Eddie Woo? Cancel Unsubscribe. Subscribe Subscribed Unsubscribe 888K.
- The purpose of the maze generation algorithm can then be considered to be making a subgraph in which it is challenging to find a route between two particular nodes. If the subgraph is not connected, then there are regions of the graph that are wasted because they do not contribute to the search space. If the graph contains loops, then there may.
A device or program used to generate keys is called a key generator or keygen.
Generation in cryptography[edit]
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender encrypts data with the receiver's public key; only the holder of the private key can decrypt this data.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and SSH use a combination of the two: one party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data used to generate it). The remainder of the conversation uses a (typically faster) symmetric-key algorithm for encryption.
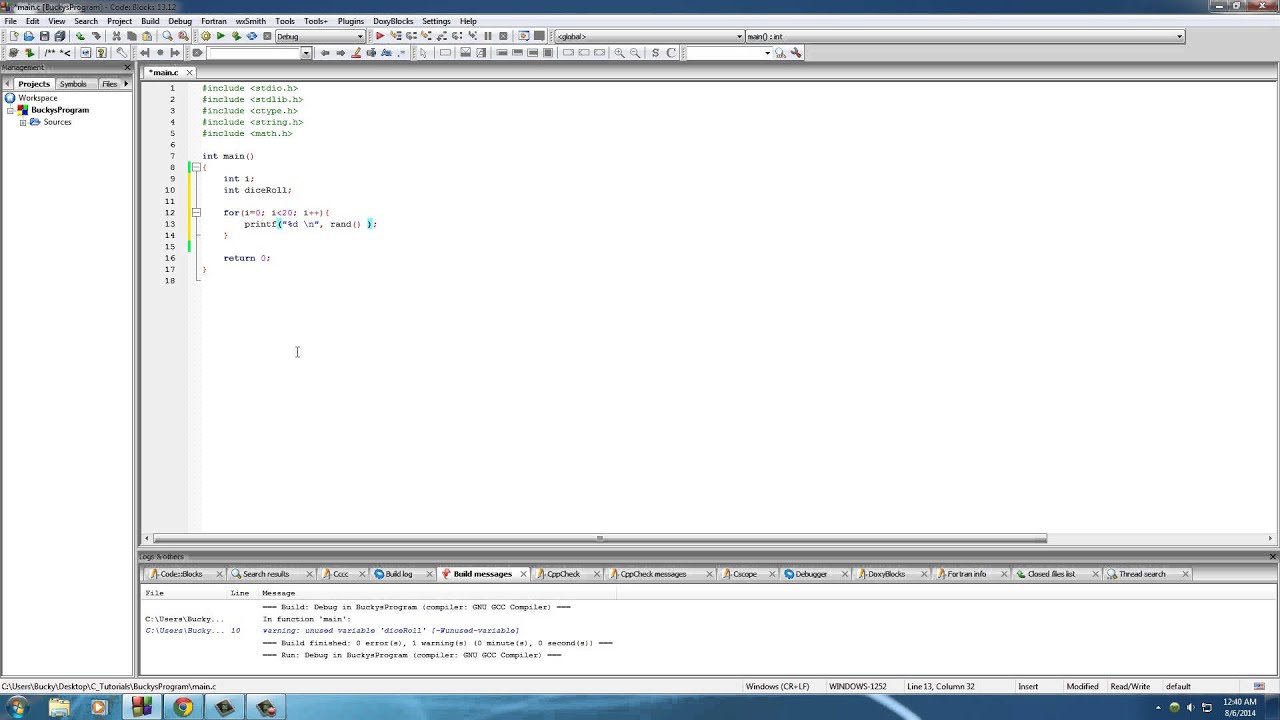
Computer cryptography uses integers for keys. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG). A PRNG is a computeralgorithm that produces data that appears random under analysis. PRNGs that use system entropy to seed data generally produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess. Another way to generate randomness is to utilize information outside the system. veracrypt (a disk encryption software) utilizes user mouse movements to generate unique seeds, in which users are encouraged to move their mouse sporadically. In other situations, the key is derived deterministically using a passphrase and a key derivation function.
Many modern protocols are designed to have forward secrecy, which requires generating a fresh new shared key for each session.
Classic cryptosystems invariably generate two identical keys at one end of the communication link and somehow transport one of the keys to the other end of the link.However, it simplifies key management to use Diffie–Hellman key exchange instead.
The simplest method to read encrypted data without actually decrypting it is a brute-force attack—simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer to attack, rendering a brute-force attack impractical. Currently, key lengths of 128 bits (for symmetric key algorithms) and 2048 bits (for public-key algorithms) are common.
Generation in physical layer[edit]
Wireless channels[edit]
A wireless channel is characterized by its two end users. By transmitting pilot signals, these two users can estimate the channel between them and use the channel information to generate a key which is secret only to them.[1] The common secret key for a group of users can be generated based on the channel of each pair of users.[2]Kaspersky 2013 key generator download.
Optical fiber[edit]
A key can also be generated by exploiting the phase fluctuation in a fiber link.[clarification needed]
See also[edit]
Random Key Generation Algorithm In C 10
- Distributed key generation: For some protocols, no party should be in the sole possession of the secret key. Rather, during distributed key generation, every party obtains a share of the key. A threshold of the participating parties need to cooperate to achieve a cryptographic task, such as decrypting a message.
References[edit]
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Feb 2016). 'Physical-Layer Secret Key Generation with Colluding Untrusted Relays'. IEEE Transactions on Wireless Communications. 15 (2): 1517–1530. doi:10.1109/TWC.2015.2491935.
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Dec 2015). 'Secret Group Key Generation in Physical Layer for Mesh Topology'. 2015 IEEE Global Communications Conference (GLOBECOM). San Diego. pp. 1–6. doi:10.1109/GLOCOM.2015.7417477.